‘Scattered Spider’ Member ‘Tylerb’ Pleads Guilty

A 24-year-old British national and senior member of the cybercrime group “Scattered Spider” has pleaded guilty to wire fraud conspiracy and aggravated identity theft. Tyler Robert Buchanan admitted his role in a series of text-message phishing attacks in the summer of 2022 that allowed the group to hack into at least a dozen major technology […]
Patch Tuesday, April 2026 Edition
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly disclosed weakness in Windows Defender dubbed “BlueHammer.” Separately, Google Chrome fixed its fourth zero-day of 2026, and an emergency update for Adobe Reader nixes an actively exploited […]
Russia Hacked Routers to Steal Microsoft Office Tokens
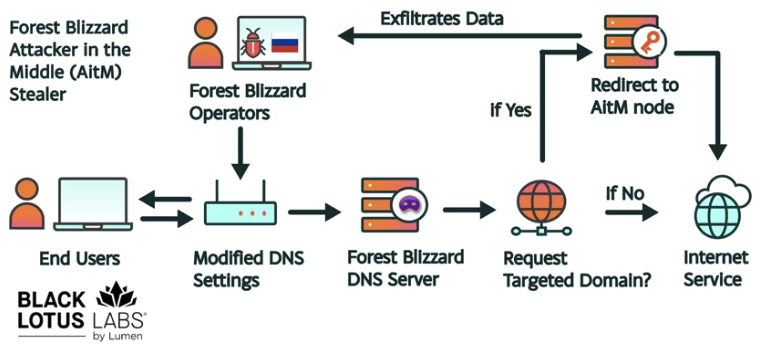
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code. Microsoft […]
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
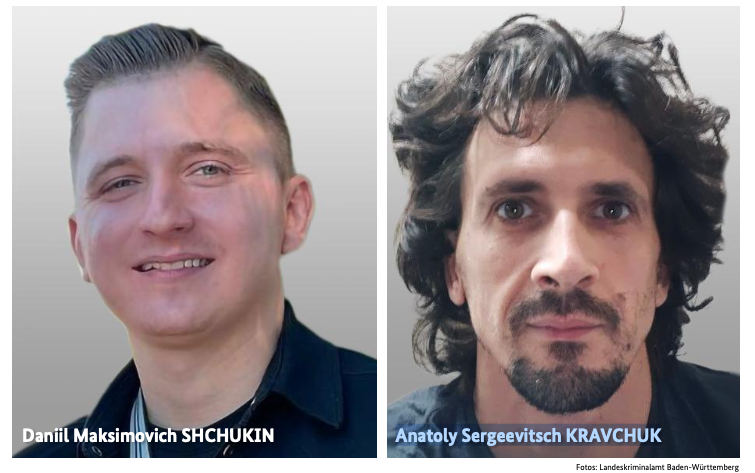
An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across […]
‘CanisterWorm’ Springs Wiper Attack Targeting Iran
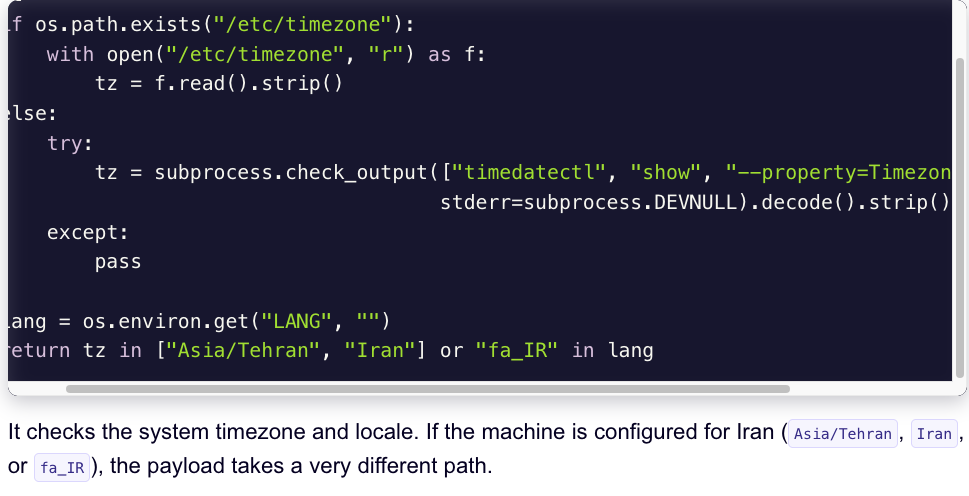
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language. Experts say the wiper campaign against Iran materialized this […]
Navigating Cloud Compliance: Essential Regulations in the Digital Age
The mass migration to cloud-based environments continues as organizations realize the inherent benefits. Cloud solutions are the technology darlings of today’s digital landscape. They offer a perfect marriage of innovative technology and organizational needs. However, it also raises significant compliance concerns for organizations. Compliance involves a complex combination of legal and technical requirements. Organizations that […]
Leveraging Microsoft Forms for Data Collection & Surveys

Data has become the lifeblood of every organization, regardless of industry or sector. Today, a business’s ability to collect, analyze, and act on data is not just an advantage, it’s essential for survival. Data-driven decision-making enables organizations to respond quickly to market changes, identify new opportunities, and improve operational efficiency. When decisions are backed by […]
How to Use AI for Business Productivity While Staying Cyber-Secure

Most organizations have realized that AI is not a sentient system looking to take over the world, but rather an invaluable tool. They have come to utilize it to improve their productivity and efficiency. AI solutions have been installed at an astounding rate. Some are used to automate repetitive tasks and to provide enriched data […]
Your Business’s Digital Compass: Creating an IT Roadmap for Small Business Growth

Small businesses often struggle to leverage technology effectively. It can be a challenge just to survive, much less thrive. In many cases, they instinctively fall back on a reactive approach to IT challenges, rather than planning and acting proactively. That’s where an IT roadmap can help. It becomes a digital compass for organizations, a strategic […]
Cracking Down on Credential Theft: Advanced Protection for Your Business Logins
During an era of digital transformation, data and security are king. That is why, as cyber threats evolve in this age of digital transformation, businesses need to be prepared. Credential theft has become one of the most damaging cyber threats facing businesses today. Whether through well-crafted phishing scams or an all-out direct attack, cybercriminals are […]
